Last updated on March 1st, 2025 at 09:50 am
One person should never have all the keys to the castle.

This post may contain affiliate links. We may earn a commission if you purchase an item through our links. It costs you nothing and helps us to fund this blog. Please see our Affiliate Disclosure & Notification for details.
The concept of Separation of Duties (also known as Segregation of Duties) applies to many different industries. The principle was developed in accounting to avoid errors and fraud but it also applies to general business practices. Although it has its beginnings in the business world, Separation of Duties has become a powerful security principle in IT and information systems.
What is Separation of Duties?
Separation of Duties is the concept of having more than one person required to complete a task.[1] Specifically, each task requires authorization from 2 different individuals or entities in order to assure integrity.
A very simple example of this would be a junior level administrator determining that a server needs to be rebooted and then asking a senior level administrator for permission to perform the reboot. Both the administrators would have to be in agreement that a reboot is the proper course of action before doing so.
How Does Separation of Duties Increase Your Security Posture?
Segregation of Duties, when properly designed, ensure that no single person has complete control over the information system environment. No one has all the keys. The requirement ensures that there is always one person checking over another.
Internal Benefits
Insider attacks are among the most common and devastating of any business or government agency. Employees, vendors, and frequent visitors who have access are much more familiar with the operations and processes in place. Insiders are aware of which services are most critical and least protected.
Segregation of Duties, especially among disgruntled employees, makes sabotage much more difficult essentially forcing them into collusion with their counterparts. The need for collusion acts as a deterrent. Would-be attackers have to share their intentions with someone else, increasing the chances of being caught or turned in.
External Benefits
In the cyber security field, the assumption is that everyone will eventually become compromised at some point. It’s not a question of if you get hacked, it’s when.
Typically when a resource or endpoint is compromised, it’s via stolen credentials. With good Segregation of Duties, one set of stolen credentials has very limited access. Not only does this mitigate the amount of damage that can be done, it also means less administrative effort for replacing that set of credentials. Services that rely on other credentials that weren’t compromised can continue to run without interruption.
Implementing Separation of Duties
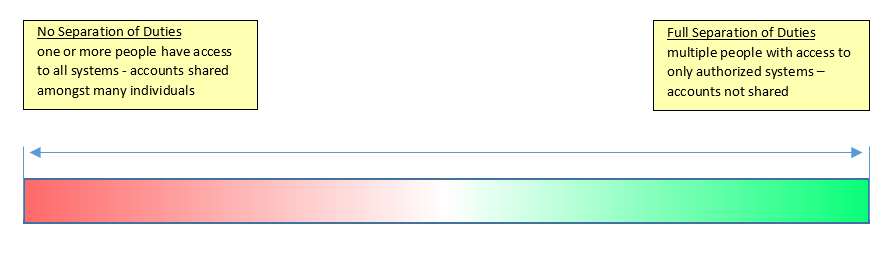
When implementing Segregation of Duties, it’s important to understand that it isn’t a binary state. It’s a spectrum where you decide how far to one side of the scale your organization needs to be.
Points to take into consideration include the size of your staff, number of systems running, importance of each system, & potential monetary losses if those systems become compromised.
Where your company or organization lives along this scale should be determined by the business owners & stakeholders, with the guidance of their technical managers. In very large environments, look to your Corporate Information Officer (CIO) for guidance.
One of the most effective ways of separating duties is to use role-based access and maintain a responsibility matrix. A responsibility matrix divides resources up into teams that you can assign individuals to and ensure that individuals aren’t assigned to 2 teams which may have a conflict of interest. Role-based security permissions will help avoid privilege creep when an employee switches teams.

In the above example the red X fields indicate exclusions that are determined by security requirements. The person responsible for equipment purchasing cannot be the person responsible for distributing the equipment. Similarly, someone responsible for managing data backups would not be the same person performing system security audits. Each team would have at least 2 different administrators assigned to it. You would also avoid pairing up the same 2 administrators in multiple blocks to avoid collusion.
Service Accounts
The same techniques applied to administrators should be applied to service accounts. These accounts, which do not have an employee name directly attached to them, should be applied with a very narrow purpose in mind.
Let’s say you have 3 SQL servers running in your environment, you would want a separate SQL service account (with unique passwords) for each server instead of a single shared one. The only administrators who would have access to these passwords would be the ones specifically assigned to the database admin team.
One of the most common mistakes for service accounts is overuse. It’s very common to find environments where a single service account is used for all services or where multiple service accounts are used but have the same password. For example, if an administrator used a service account that had access to everything to steal information or sabotage the company, it would be difficult to pin that act on someone specific if many people have access to it.
Challenges to Productivity Introduced by Separation of Duties
Because of the inverse relationship between security & productivity, finding a balance can be difficult to achieve. This is one of the most challenging aspects of the IT world today. As cyber security becomes more important, meeting the demands of customers without sacrificing the company mission becomes more difficult. Increasing Segregation of Duties typically increases your operations costs. The increased costs should be justified by a higher security posture and better damage mitigation.
Large Businesses
While some decisions are typically made by one person (server reboots for example), critical decisions must wait for multiple approvals before implementation. This can potentially hinder response times for requests.
In cases where your responsibility matrix has many conflicts of interest, you may find that you have to budget for additional personnel. If your responsibility matrix has a lot of teams with many security exclusions, be prepared to change your management paradigm as to what constitutes sufficient quantity & quality of work. As their access becomes more limited, your employees will have more downtime. During a serious outage, you may even see some staff members seemingly unresponsive. Keep in mind that downtime is what allows tasks to be properly prioritized. The resulting calendar white space allows for rescheduling existing tasks when an emergency occurs. During outages, if everyone is running around in hair-on-fire mode, it usually takes longer to resolve the issue.
Small & Medium Businesses
For small businesses, the challenges with Separation of Duties are greater. A company that has just 1 or 2 systems/network administrators may simply not be able to divide them up. In these environments, having regular audits performed by an outside entity is key.
Service accounts can still be broken up and security logs should be kept out of administrator reach so that auditors can fully understand what the staff is doing.
Taking advantage of vendor-provided support on specific systems will also help. Many enterprise level hardware systems come with vendor support as part of the purchase and warranty price. These support plans can include maintenance and remote support that virtually eliminate the employee need to interact with the system. Essentially, you’re assigning the support vendor to one of the teams defined in the Separation of Duties responsibility matrix.

How is Separation of Duties Likely to Affect Your Staff?
If your company is instituting Separation of Duties as a new initiative, it’s important to communicate to existing support staff why their access to systems is being limited. You want to avoid making them feel as if they’re being unnecessarily restricted. Staff members who have formal infosec training will understand while others may need more explanation.
Allow the employees some input as to which teams they will be on. This will allow them to focus their energy on the technologies that interest them the most. Some teams will have more downtime than others.
Try to mix team memberships to ensure downtime is spread evenly throughout the workforce. Having one team that’s overworked while another has nothing to do all day will be detrimental to the overall benefit provided by Separation of Duties.
Lastly, while many employees appreciate the increase in downtime and ability to focus on individual tasks, incorporating Separation of Duties is likely to leave some of your staff bored. These staff members are usually the most ambitious and motivated ones; they’re high-energy and want to learn everything. Individuals like this are valuable to your organization so you need to avoid having them leave for a more stimulating job somewhere else. Ensure they’re put on teams that have little conflict of interest with other teams, as it will allow you to put them on a greater number of projects without sacrificing the security introduced by Separation of Duties. You can also provide them with non-technical tasks such as training new employees.
The Path to Profit
Instituting Separation of Duties can be costly. Many companies have trouble justifying such a security protocol. For very small businesses, there may be no way to justify the cost. The amount of money lost during an internal sabotage or external attack should outweigh the expense. Accounting systems have used the principle for decades to avoid fraud and theft. As more and more of our business comes to rely on technology, the cybersecurity world should be no different.
Sharif Jameel is a business owner, IT professional, runner, & musician. His professional certifications include CASP, Sec+, Net+, MCSA, & ITIL and others. He’s also the guitar player for the Baltimore-based cover bands, Liquifaction and Minority Report.

Pingback: Privilege Creep: Prevention & Correction - Website Design Baltimore | SEO Baltimore | CGS Computers